OWASP Broken Web Applications Project
Open Web Application Security Project (OWASP) Broken Web Applications Project, a collection of vulnerable web applications that is distributed on a Virtual Machine in Vmware.
OWASP Broken Web Applications Project
The OWASP Broken Web Applications Project (OWASP BWA) serves as a “living museum” of vulnerabilities. It is considered a classic, cornerstone resource that is essential for anyone aiming to master Web Penetration Testing.
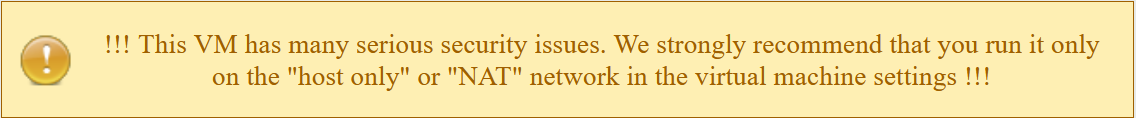
Technically, it is a Virtual Machine (VM) based on an older Linux distribution (typically Ubuntu), which has been intentionally pre-packaged with a wide variety of web applications containing known security flaws.
⚠️ Project Status: Legacy Although major updates ceased around 2015, this project remains highly relevant. The fundamental logic behind vulnerabilities (such as SQLi, XSS, and Command Injection) does not change over time. It provides a convenient, centralized environment to practice these concepts without the hassle of manually installing multiple vulnerable apps.
What Will You Learn? (The Attack Vectors)
When engaging with this system, you are effectively performing Gray Box or White Box Testing (since the source code is often available for review). You will manually execute and master the following attack vectors:
-
SQL Injection (SQLi):
- You will learn how to Dump the Database manually and by using automation tools like
sqlmap. - Understand the critical difference between Blind SQLi and Error-based SQLi.
- You will learn how to Dump the Database manually and by using automation tools like
-
Cross-Site Scripting (XSS):
- Experiment with all three main types: Reflected, Stored, and DOM-based.
- Execute practical scenarios, such as stealing Session Cookies to hijack user accounts.
-
Command Injection:
- Learn how to force the server to execute arbitrary Linux commands (e.g.,
cat /etc/passwd) directly through vulnerable input fields.
- Learn how to force the server to execute arbitrary Linux commands (e.g.,
-
File Upload Vulnerabilities:
- Practice bypassing restrictions to upload a malicious Shell (e.g.,
php-reverse-shell). - Establish a full remote connection, such as a Meterpreter Session, to gain control over the server.
- Practice bypassing restrictions to upload a malicious Shell (e.g.,
Why is it Important for a Future Expert?
This project teaches you how to handle Legacy Systems.
In the real world, not every company uses the latest technology. You will encounter major institutions—such as banks and airlines—that still rely on infrastructure similar to what you find in OWASP BWA.
Training on this environment gives you the flexibility to deal with old, “decaying” systems, which often represent the Weakest Link in an organization’s security posture and the primary entry point for attackers.
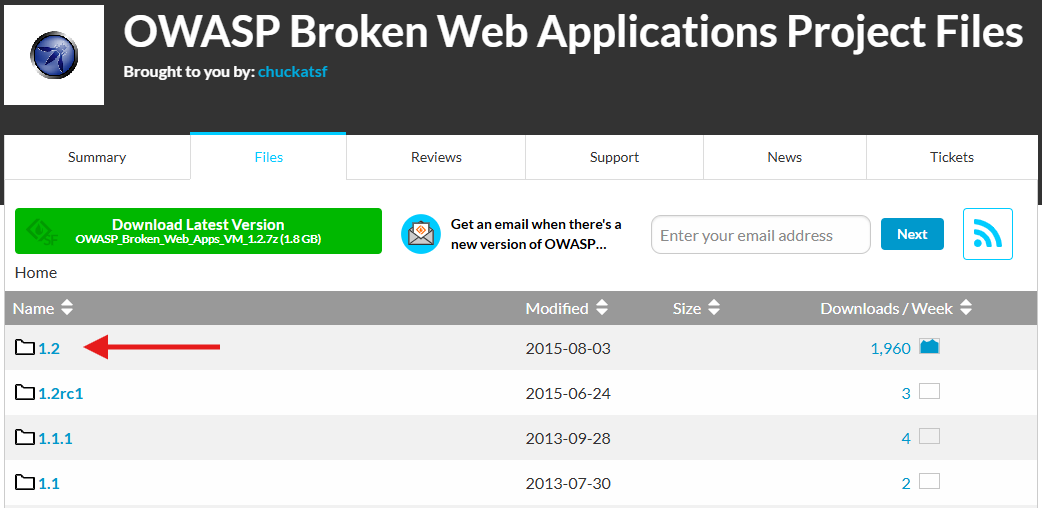
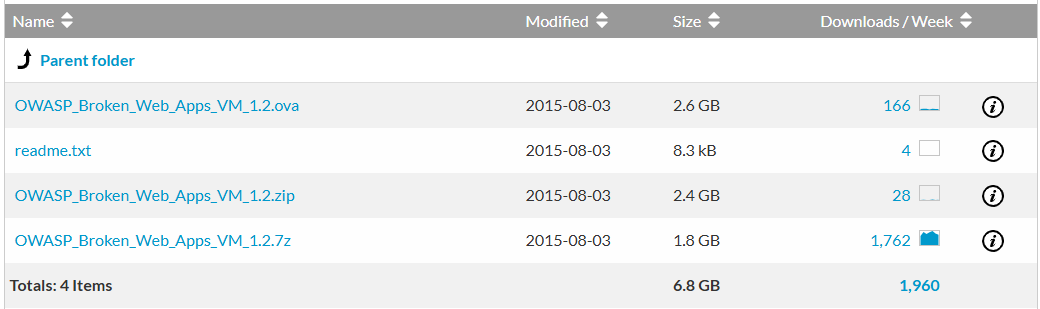
Download & Version
For this lab environment, we are utilizing the latest version available. You can download the full Virtual Machine compressed file (usually .7z or .zip) directly from the official repository.
** Official Download Link:** OWASP Broken Web Applications Project - SourceForge
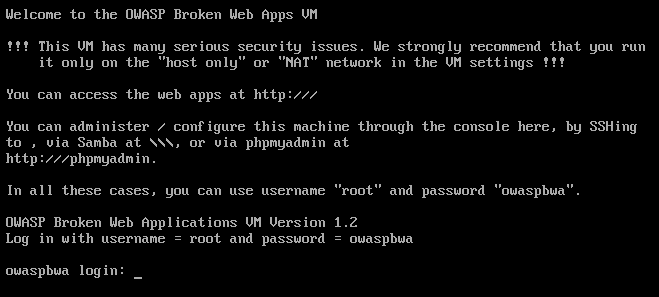
and access the web applications using the ip for Machine
⚠️ important note

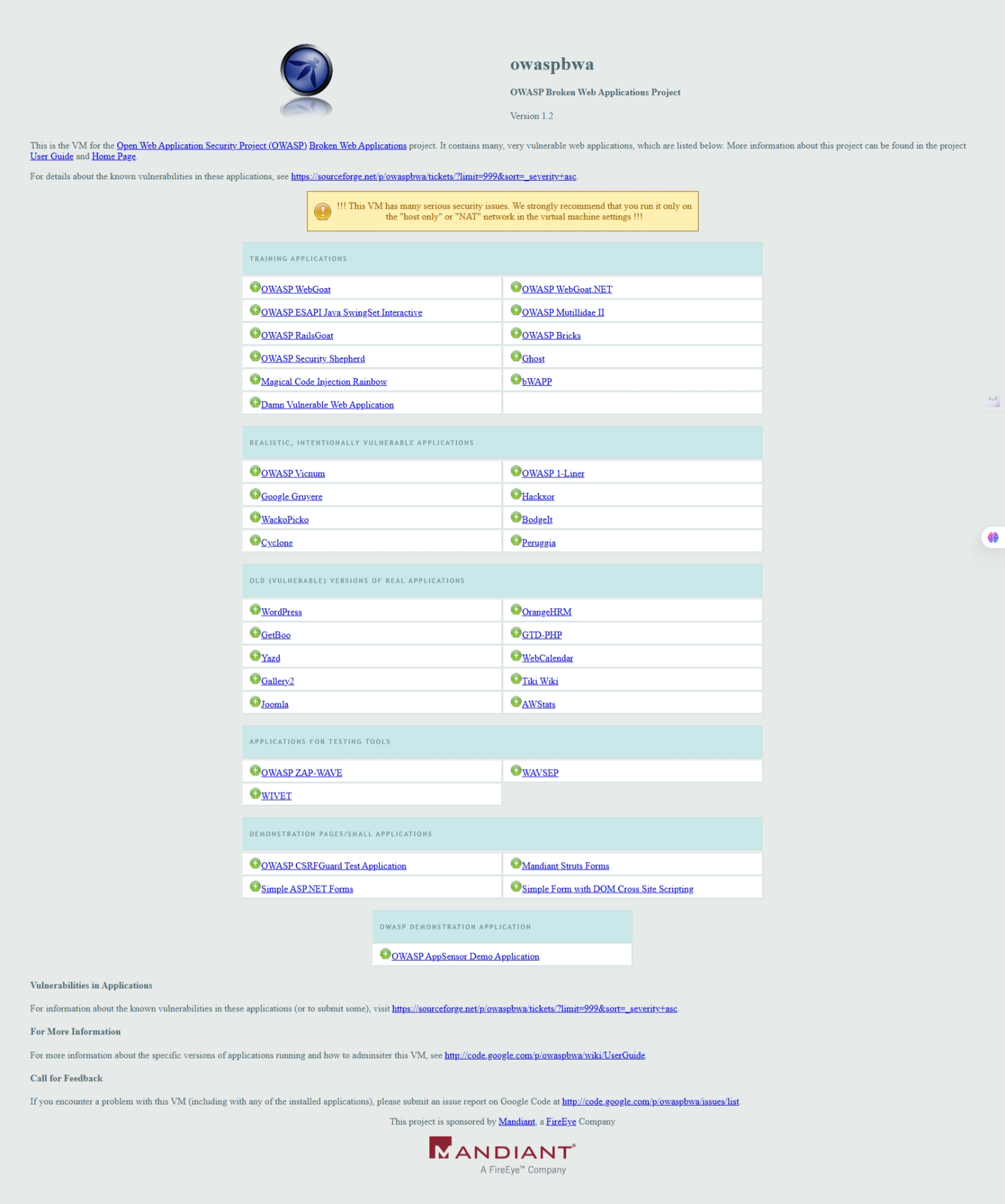
Training Applications: Intentionally Broken
The list above represents the Training Applications. The fundamental difference between these and real-world legacy applications is intent: these apps were designed to be broken.
The developers here did not commit errors; they deliberately left the doors open to teach you how to walk through them.
Below, we will conduct a quick, intensive Reconnaissance tour of each target on this list. We will analyze what each application hides technically and adopt the Attacker’s Mindset to understand how a hacker views these targets.
1. The Classics
These applications are the foundation. If you do not master these, do not proceed to the advanced targets.
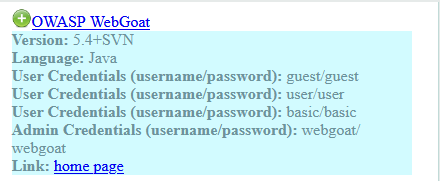
OWASP WebGoat (Java)
- Tech Stack:
Java/J2EE. - Analysis: This is the “Godfather” of vulnerable apps. It is strictly educational and structured into lessons. It doesn’t give you full freedom; instead, it holds your hand through specific scenarios.
- Learning Outcome: It focuses heavily on Business Logic Flaws, Access Control, and manipulating complex Java Parameters. It is excellent for understanding how large enterprises approach security.
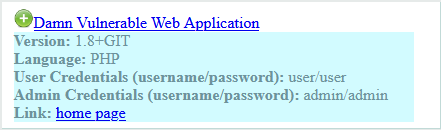
Damn Vulnerable Web Application (DVWA) (PHP)
- Tech Stack:
PHP/MySQL. - Analysis: Arguably the most famous training app in history. Its unique feature is the “Magic Button” that allows you to toggle difficulty levels (Low, Medium, High, Impossible).
- Learning Outcome: It teaches you the battle between Sanitization (Developer’s defense) and Bypassing Filters (Attacker’s offense). It is the essential “Gym” for mastering SQL Injection and XSS.
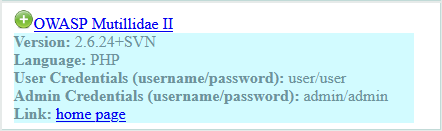
OWASP Mutillidae II (PHP)
- Tech Stack:
PHP. - Analysis: A comprehensive platform containing over 40 types of vulnerabilities. It simulates a real-world environment with a blog, voting system, and user accounts.
- Learning Outcome: It covers the entire OWASP Top 10. Its key advantage is that it is stable enough to test Automated Scanners (like Burp Suite or OWASP ZAP) to observe how they interact with a target.
2. The Encyclopedias
These applications contain a massive number of vulnerabilities, meticulously categorized.
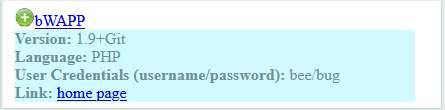
bWAPP (buggy Web Application) (PHP)
- Tech Stack:
PHP. - Analysis: This is often the preferred choice for advanced training. It covers over 100 distinct vulnerabilities.
- Learning Outcome: It goes beyond basics, teaching modern and complex flaws like Heartbleed, Shellshock, SSRF (Server-Side Request Forgery), and HTML5 issues. Mastering bWAPP effectively makes you market-ready.
3. Language Specific Targets
A professional hacker knows that vulnerabilities in PHP behave differently than those in .NET or Ruby.
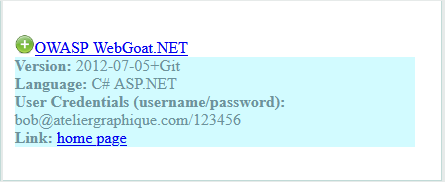
OWASP WebGoat.NET (C# ASP.NET)
- Target:
Microsoft Environment. - Learning Outcome: You will learn about ViewState Manipulation, Code Injection in IIS, and Entity Framework vulnerabilities. This is essential for pentesting companies relying on the Microsoft Stack.
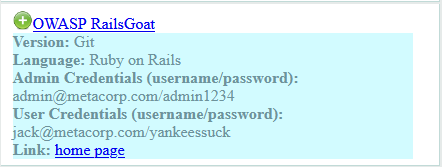
OWASP RailsGoat (Ruby on Rails)
- Target:
Ruby Environment. - Learning Outcome: Ruby has unique flaws, such as Mass Assignment (changing user privileges by passing an extra parameter). You rarely encounter this specific behavior in PHP environments.
4. Vulnerability Specific Apps
These are designed to teach you “one move” but with absolute mastery (Bruce Lee style).
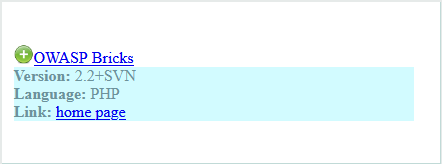
OWASP Bricks (PHP)
- Specialization: SQL Injection (SQLi) only.
- Analysis: It provides various injection scenarios, ranging from very easy to complex filter evasion. If you want to become a Database Wizard, start here.
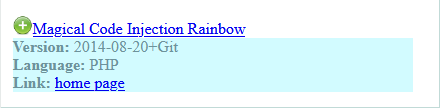
Magical Code Injection Rainbow (MCIR) (PHP)
- Specialization: Injection Attacks (SQL, XSS, LDAP, Command).
- Analysis: Designed specifically to test the detection capabilities of Scanners and to practice manual Payload Crafting.
5. Defense & CTF
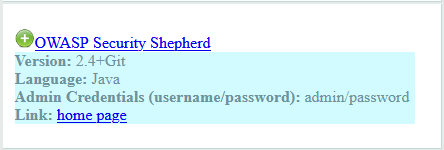
OWASP Security Shepherd (Java)
- Type: CTF (Capture The Flag) Platform.
- Analysis: It teaches security through gamified challenges (Levels & Points). It covers both Web and Mobile Web. It emphasizes Hardening (how to protect the system) rather than just breaking it.
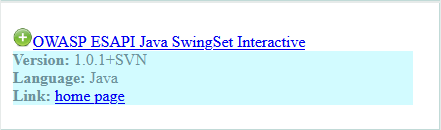
OWASP ESAPI Java SwingSet Interactive
- Type: Pure Defense.
- Analysis: It demonstrates how to use the ESAPI (Enterprise Security API) library to patch vulnerabilities. Here you see the “Solution” and how secure code should actually be written.
6. The Miscellaneous (Ghosts)
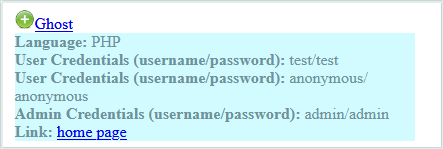
Ghost
- Analysis: A very simple PHP application. Based on its default credentials (
test/test,admin/admin), it is an ideal target for learning Brute Force attacks, Login Bypasses, and basic File Upload vulnerabilities.
Recommended Learning Path (Roadmap)
To maximize your learning efficiency, I recommend following this tiered approach. Do not jump to complex frameworks before mastering the basics of HTTP and simple input handling.
Level 1: The Fundamentals (Start Here)
Focus on understanding what a vulnerability looks like in its simplest form, with minimal code complexity.
- Damn Vulnerable Web Application (DVWA)
- OWASP Bricks
Level 2: The Deep Dive (Breadth & Tools)
Expand your knowledge to cover a wider range of vulnerabilities (100+) and start practicing with automated tools like Burp Suite.
- bWAPP
- OWASP Mutillidae II
Level 3: Enterprise Stacks (Logic & Architecture)
Shift your focus to heavy, enterprise-grade languages (Java & .NET) where vulnerabilities often lie in business logic and complex configurations rather than simple syntax errors.
- OWASP WebGoat (Java)
- OWASP WebGoat.NET
Level 4: The Specialist (Niche & CTF)
Master specific frameworks and engage in gamified security challenges to test your defense and advanced injection skills.
- OWASP RailsGoat
- OWASP Security Shepherd
- Magical Code Injection Rainbow (MCIR)
Expert Tips for Survival
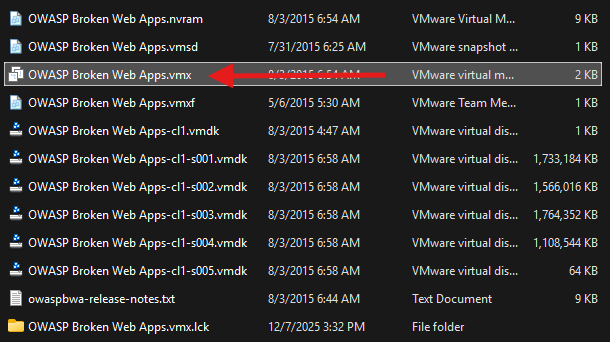
1. The Time Machine (Snapshots)
This is the single most critical technical advice. You are dealing with malicious payloads and destructive SQL injections that can wipe databases or corrupt the file system.
- The Action: Before you launch a single attack, go to your VMware/VirtualBox settings and take a Snapshot. Name it
Fresh Install. - The Benefit: If (and when) you break the OS, you can revert to a clean state in seconds. Never work without a safety net.
2. Service Management (Reviving the Dead)
Since these are legacy applications running on old kernels, services like Apache or MySQL often crash under the stress of automated scanners (Fuzzing). If a site goes down, do not reboot the entire VM immediately.
- The Fix: Log in as
rootvia the terminal and restart the specific service:
service apache2 restart # For PHP/General Web Server issuesservice mysql restart # If the Database connects failservice tomcat6 restart # For Java apps (WebGoat)3. do not update the system
📚 References & Resources
- OWASP Vulnerable Web Applications Directory
- Description: The official directory. Visit this to find detailed documentation, usage guides, and standalone versions of specific vulnerable applications if you wish to run them outside the VM.
- OWASP Projects Main Page
- Description: The central hub for all OWASP initiatives. Here you can find the latest tools, standards (like the Top 10), and documentation updates.